Cisco Umbrella Block Page !full! -
Ultimately, the effectiveness of the block page is a litmus test for an organization's security maturity. A rigid, opaque block page signals a culture of "no." A clear, informative, and flexible block page signals a culture of "safe and informed yes." As Cisco continues to evolve Umbrella, the block page remains a humble but powerful reminder that even in a zero-trust world, communication is as critical as control.
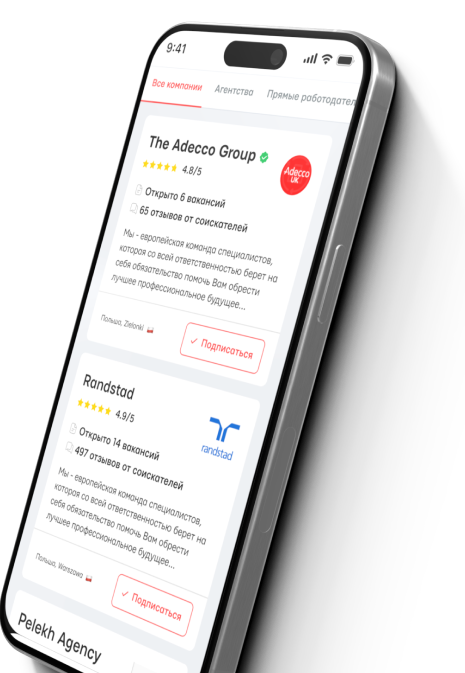
In the modern cybersecurity landscape, prevention is paramount. As organizations adopt cloud-delivered security solutions, Cisco Umbrella stands out as a leading Secure Web Gateway (SWG) and DNS-layer security tool. Central to its operation is a simple but crucial component: the block page . This essay explores the Cisco Umbrella block page, arguing that while it serves as an essential technical control for enforcing security policies, its design, customization, and psychological impact on users significantly determine the balance between organizational security and workplace productivity. Purpose and Functionality At its core, the block page is the user-facing manifestation of a security decision. When a user attempts to navigate to a domain or URL that violates an organization's policy—whether due to malware, phishing, command-and-control (C2) callbacks, or simply a prohibited category like social media or adult content—Cisco Umbrella intercepts the request. Instead of resolving the DNS query to the intended IP address, Umbrella returns an IP address that points to its own block page server. The user’s browser then displays a page stating that access has been blocked. cisco umbrella block page
Cisco Umbrella's standard block page is relatively clean. It displays a large red or yellow "Blocked" banner, the category name (e.g., "Phishing"), and a brief explanation. However, a common criticism is that it can still be alarming to non-technical users, especially when security threats are cited. An employee accessing a harmless news site that has been temporarily compromised might see a "Security Threat" block, leading to unnecessary panic. Ultimately, the effectiveness of the block page is
Another limitation is that the block page only triggers on explicit HTTP/HTTPS requests. Applications that use non-web protocols or hardcoded IP addresses may not render an HTML block page, leaving users confused about why a service is failing. The Cisco Umbrella block page is far more than a simple roadblock. It is a strategic communication tool that sits at the intersection of security enforcement, user psychology, and operational efficiency. When left in its default state, it effectively blocks threats but risks frustrating users. When properly customized with branding, clear policy language, and a judiciously used override feature, it transforms into a collaborative interface that educates users, reduces IT tickets, and maintains productivity. Purpose and Functionality At its core, the block
Critically, administrators can enable an . This allows a technically savvy or authorized user to temporarily bypass a block by entering a valid justification and their Active Directory credentials. The override is logged, providing an audit trail. This feature transforms the block page from a simple barrier into a workflow tool , acknowledging that legitimate websites can sometimes be miscategorized (false positives) or that a researcher may need access to a typically prohibited site for valid work purposes. User Experience (UX) and Psychological Impact The design of the block page directly influences user behavior and organizational friction. A generic, technical error message—like "DNS resolution failed"—often leads to frustration, help desk tickets, or attempts to circumvent security using personal devices or proxies. Conversely, a clear, branded block page reduces confusion.
However, the block page itself introduces a potential vulnerability: . For HTTPS sites, the block page must be presented before the secure connection is established. If an administrator is not careful, they might configure SSL decryption to bypass certain categories to avoid certificate errors, inadvertently creating a security gap. Furthermore, advanced malware can sometimes detect the presence of a block page and modify its behavior (e.g., using DNS over HTTPS or changing domains), rendering the block page irrelevant as a feedback mechanism.
To improve UX, organizations should leverage custom messages. For example, instead of "Access to Social Media is Prohibited," a better message might read: "Social media access is limited to lunch hours. Please contact HR for exceptions." This shifts the perception from arbitrary IT control to a clear, organizational policy. From a security perspective, the block page is a double-edged sword. Positively, it provides valuable feedback to security teams via the logs generated from blocked requests. High volumes of block events for specific domains can indicate a malware outbreak or a user clicking on a phishing link.